When you are a vendor who provides a valuable service, you look for opportunities to help companies. Sometimes, a vendor’s claims can be exaggerated or even contrived. For that reason, we refer to trusted third-party data to make our point. This month we will use the FBI’s annual Internet Crime Report to show the continued rise of social engineering attacks in the US, especially through voice phishing, or as its commonly referred, vishing.
The FBI’s Internet Crime Complaint Center tracks cybercrime complaints and data each year and compares the result from the previous five years. As one might expect, both the number of complaints and the financial losses to cybercrimes has increased each year.
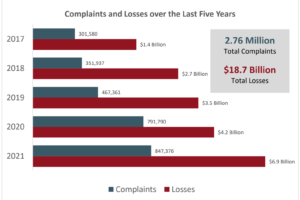
Figure 1: Increase in Complaints and Financial Loss
The report breaks down the crime types into thirty different categories including denial of service, computer intrusion and gambling. However, the majority could be considered scam or social engineering related. Among the scams, the FBI includes Romance Scams, Rental Scams and the largest category, Phishing/Vishing/SMiShing/Pharming.
Social Engineering Is the Top Risk
This FBI report graph shows just how much the social engineering category outweighs even the next four most common crime types.
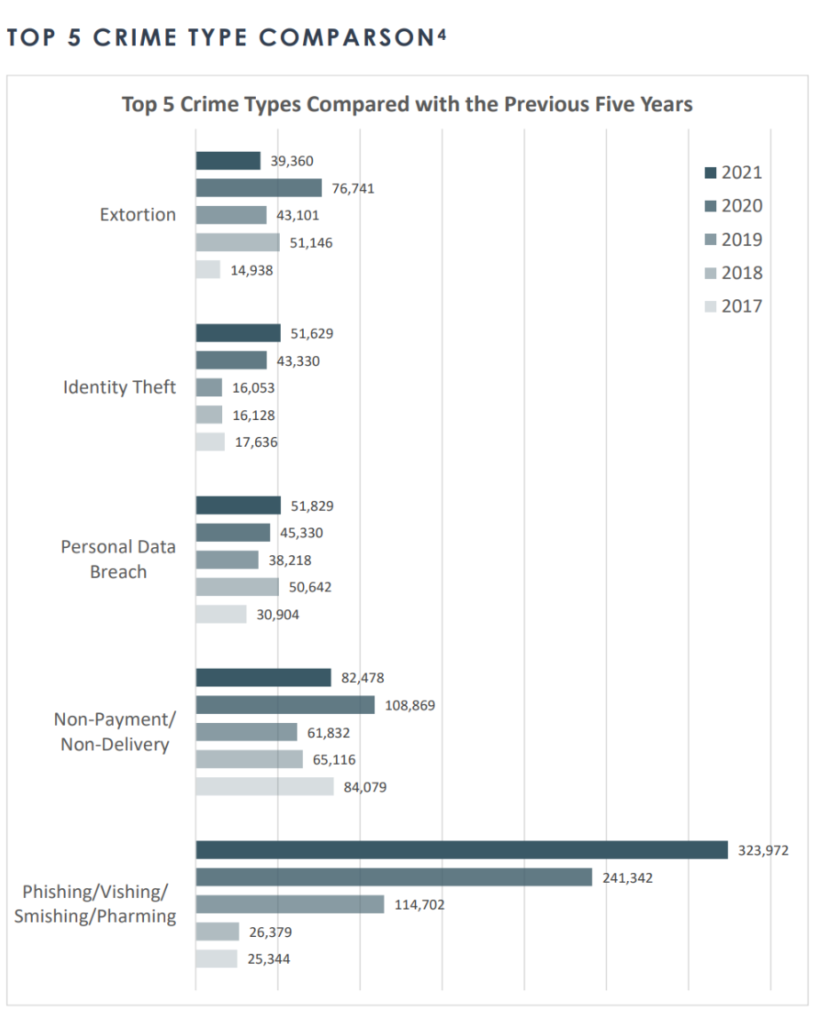
Figure 2: Top Five Most Common Internet Crimes
Most are aware of phishing as a malicious attack that often comes through a messaging service like email. Vishing is voice phishing, where an attacker tries to elicit sensitive information or action over the phone. SMiShing is similar to phishing but uses SMS, or text messages.
The last category, pharming, can be difficult to understand its difference from phishing, as both will often include a lookalike or fake web page that steals data. The real difference between the two is how the victim arrives at the page. With phishing, the victim will be directed to the data-stealing page by a message of some type, often an email. In a pharming attack, the victim will arrive at the page passively, such as by search results, purchased advertising, or a watering hole attack. Instead of the attack being targeted through a message like an email or text, the attack sits passively, letting interested and unaware victims walk right in.
The Hidden Aspect of Social Engineering
The FBI report also includes other attack types, including Business Email Compromise (BEC) and Ransomware. These are two other attack vectors we hear about often. These are both legitimately concerning attacks for businesses and keep security practitioners awake at night. However, there is an aspect to them that is often overlooked, the initial vector to these attacks. How does an attacker send emails from inside a business executive’s mail account? How does an attacker get sufficient access to a network to install ransomware? That initial threat vector is often through social engineering.
The attackers may use a phishing email to obtain a password to a mailbox. Once they have access to the victim’s mailbox, the attackers can send trusted emails within the company. If your job is to pay invoices and the Chief Financial Officer sent you an email from their corporate account and asked you to pay an invoice, you likely would do it. If a high-level manager sends an email asking for information on employees, salaries, customers or the latest project, the recipient will trust that email and respond. This is how a BEC can be devastating to a company.
Malware and Ransomware
Malware and ransomware also will often find a foothold through social engineering. Attackers may try to attach the malware to an email, but modern email filters are doing a much better job of blocking those attacks. Another vector is to load the malware from a web site after the victim clicks on a link.
Tech Support Fraud (TSF)
A third method attackers use is through what the FBI refers to as Tech Support Fraud (TSF). Over the last five years, the FBI has reported a huge increase in TSF financial losses from $14 million in 2017 to more than $347 million in 2021. The way that TSF can play a role in malware and ransomware infections is the attacker calls employees as a trusted member of the IT department and gets the employee to install remote access software on their computer. Once the software is installed, the attacker has full access to the workstation, the same access as if they were sitting in the employee’s seat. The attacker can then install the ransomware, force it to propagate through the network, locking up vital resources within the company.
Educate and Test Your Employees
We know that cybersecurity intrusions are a problem, and this FBI report indicates they are increasing. Where problems of past years have been in the software and lack of updates and patching, now they are more human-based. IT departments have done an outstanding job of hardening their networks to technical attacks. However, companies now need to be more focused on the employees. Companies need to focus more on education and testing of the human attack vector. As the FBI report showed, social engineering is currently the top risk, and it is increasing.
To test your employees against vishing and phishing attacks or even from an on-site physical access compromise see how Social-Engineer, LLC can help you.
At Social Engineer LLC, our purpose is to bring education and awareness to all users of technology. For a detailed list of our services and how we can help you achieve your information/cybersecurity goals please visit: